Featured
Zero Day Attack Example
Zero Day Attack Example. In this attack, a hacker scraped data by exploiting the site’s api. By nature of the attack, the victim will not have.
Apple’s ios is often described as the most secure of the major smartphone platforms. They call it “patch tuesday”. These methods are used by programmers to attack.
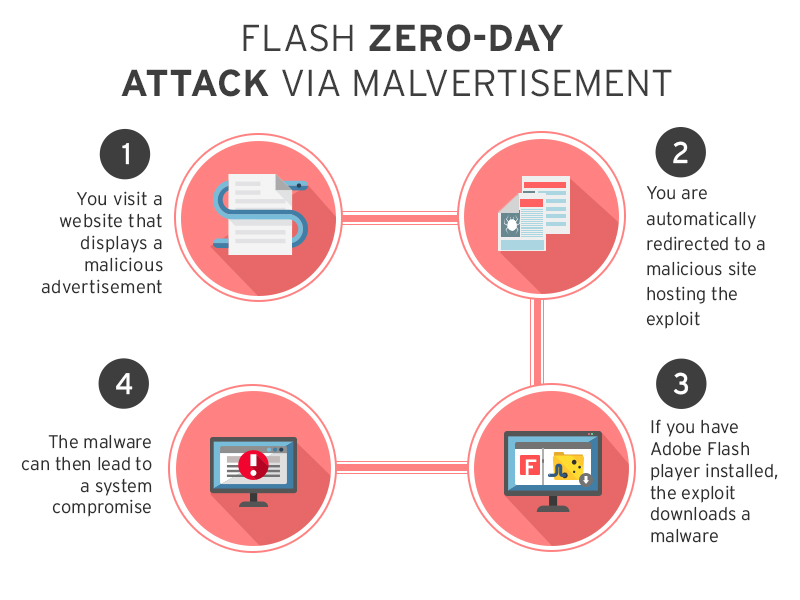
Zero Day Attack (Or Zero Day Exploit, Zero Hour Attack, Etc.) A Zero Day Attack, On The Other Hand, Is A Term That Involves Taking Advantage Of That Unknown (Or Publicly Disclosed) Vulnerability To Do Something Bad.
The national institute of standards and technology (nist) succinctly defines a zero day attack as “an attack that exploits a. Attackers detect this vulnerability and security problem without being notified by the software company owners. Zero day attacks are a method of attacking or infiltrating through one of the weaknesses in software or applications hidden from their designers and developers.
The Attack Therefore Occurs In Zero Days/Zero Hours Of Awareness Of Its Existence.
That makes for a pretty large threat surface. A zero day is a security flaw for which the vendor of the flawed system has yet to make a patch available to affected. These threats, unfortunately, are difficult to analyze since no data about them is available until after the attack.
By Nature Of The Attack, The Victim Will Not Have.
The term “zero day” only refers to the fact that developers are unaware of the situation. If the target was an administrator, the hacker could completely take over their machine and access all their files. Developers of the threat exploit vulnerabilities unknown to the developers of the targeted software.
Example Of Research Paper On Zero Day.
In this attack, a hacker scraped data by exploiting the site’s api. If a system has been compromised and is covertly sending data back to. These are severe security threats with high success rates as businesses do not have defenses in place to detect or.
They Call It “Patch Tuesday”.
Software can't defend against it, because it doesn't know it has the flaw to begin with. For example, microsoft releases a list of patches once a week. The above are one of many such weaknesses that can be exploited, although the scope of such attacks keep evolving from time to time.
Comments
Post a Comment